Google has released emergency updates to fix a serious Chrome vulnerability exploited in zero-day attacks. This is the first security flaw to be fixed since the beginning of this year.
“Google is aware that an exploit for CVE-2026-2441 exists in the wild,” Google said in a statement security advice released on Friday.
According to the Chromium commit history, this use-after-free vulnerability (reported by security researcher Shaheen Fazim) is due to an iterator invalidation bug in CSSFontFeatureValuesMap, Chrome’s implementation of CSS font feature values. Successful exploitation could allow attackers to cause browser crashes, display issues, data corruption, or other undefined behavior.

The commit message also notes that the CVE-2026-2441 patch addresses “the immediate issue” but notes that “remaining work” is being tracked in bug 483936078suggesting this may be a temporary solution or related issues still need to be addressed.
The patch was tagged as “cherry-picked” (or backported) for multiple commits, indicating that it was important enough to include in a stable release rather than waiting for the next major version (likely because the vulnerability is being exploited in the wild).
While Google has found evidence that attackers have exploited this zero-day flaw in the wild, it has not shared any additional details about these incidents.
“Access to bug details and links may be kept restricted until the majority of users have been updated with a fix. We will also enforce restrictions if the bug exists in a third-party library that other projects similarly depend on but has not yet been fixed,” the report said.
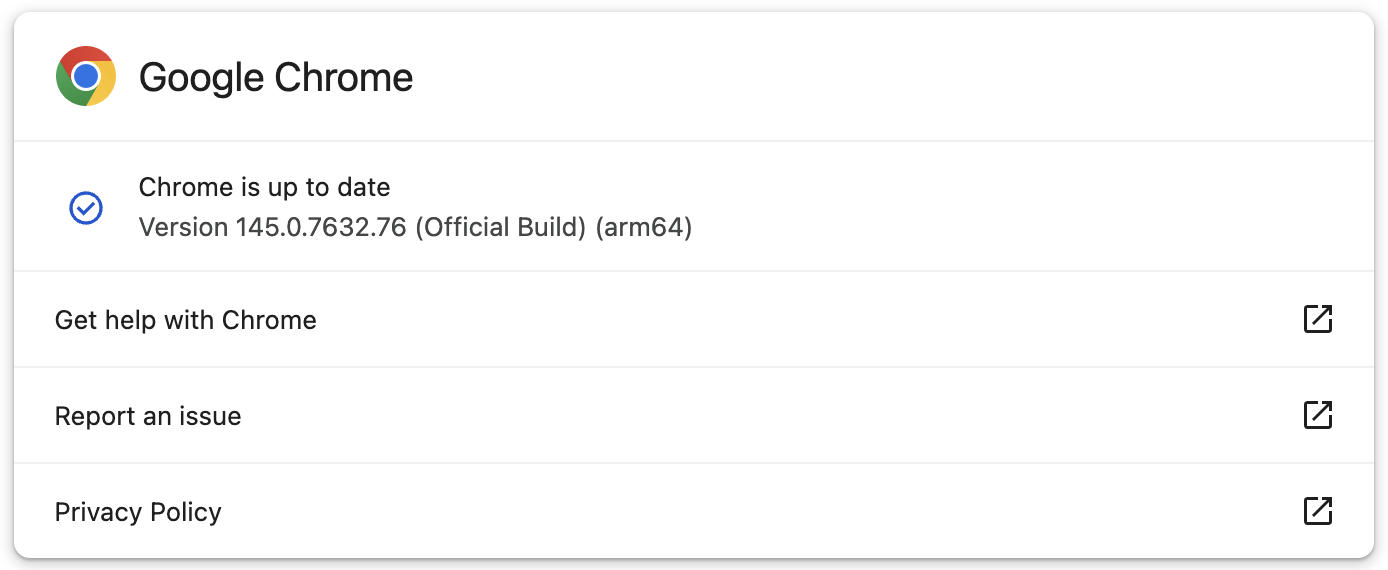
Google has now fixed this vulnerability for users in the Stable Desktop channel, with new versions rolling out globally to Windows, macOS (145.0.7632.75/76), and Linux (144.0.7559.75) users in the coming days or weeks.
If you don’t want to update manually, you can also let Chrome automatically check for updates and install them after the next launch.
While this is the first actively exploited Chrome vulnerability patched since early 2026, Google addressed a total of eight zero-days exploited in the wild last year. Many of these were reported by the company’s Threat Analysis Group (TAG), widely known for tracking and identifying zero-days exploited in spyware attacks targeting high-risk individuals.

Modern IT infrastructure moves faster than manual workflows can handle.
In this new Tines guide, you’ll learn how your team can reduce hidden manual delays, improve reliability through automated response, and build and scale intelligent workflows on top of the tools you already use.
#Google #fixing #Chrome #zeroday #exploited #attacks #year




