You already have enterprise-grade infrastructure protection via the native security functions from Kinsta via isolated containers, a cloudflare Enterprise WAF, SOC 2 type II compliance and mandatory Mykinner Two factor authentication (2FA).
However, infrastructure protection is only half the comparison. WordPress Security Workflows are needed to stop the advanced attacks that direct the platform directly on the vulnerabilities of the plug -and compromise your references.
This guide shows how to build the security workflows that use the native possibilities of Kinsta and at the same time implement a number of essential protection at WordPress level.
Two-factor authentication (2FA) for administrators, customers and staff
Kinsta Mandates 2fa for Mykinnsta Access, which is a good start when securing your hosting infrastructure. This protects server configurations, invoicing, implementation tools and everything you use to manage your servers and sites.
However, WordPress works independently. For example, attackers who focus on wp-login.php Will completely bypass Mykinner. Even with locking the infrastructure of Kinsta, valid WordPress references provide immediate end access to the person who has them without extra verification.
The distinction is crucial: Mykpersta 2FA protects access to the hosting account (SSH, staging, backups and more), while WordPress 2FA protects access to content management. As such you must need it Both layers To protect the whole of your site.
Implementation of WordPress 2FA in addition to Kinsta infrastructure protection
The use of a plug -in to add 2FA for your website is an almost necessary step. There are many options available from some of the leading developers in WordPress. The first option is Two -factorfrom the WordPress.org team.

It is a simple solution that offers time-based one-time passwords (TOTP), Fido Universal 2nd Factor (U2F), e-mail codes and even a dummy setup for testing. There are also numerous actions and filters for more integration.
For other options you have a large number of solutions:
- You can WP 2FA Plug -in melapress to force 2FA for all user roles and at the same time offer decorative periods for onboarding. The plug -in supports TOTP apps (such as Google Authenticator and Authy), E -Mail codes and back -up methods. Premium functionality adds trusted devices and white labels.
- Wordfence -Loglog protection is a spin-off of the core plug-in and offers independent authentication without the entire security suite. It remembers 30 days before devices and includes Recaptcha V3. The plug-in also works with custom login pages and XML-RPC, which is crucial for mobile apps and external publication.
- The Mininorange SSO Plug -in is great for Enterprise environments because it connects WordPress with identity providers such as Azure Ad, Google Workspace and Okta. Directory groups have also been automatically mapped to WordPress roles, so marketing receives editorial access, support receives contributing privileges, and so on.
What is more, these plug -ins are all free and have fast installation times.
Set up real-time reports with webhooks and monitoring
Kinsta offers infrastructure monitoring as a core service: uptime checks every three minutes from ten worldwide locations, detection of performance -anomalie and e -mail reports for malfunctions. There is also the activity log that keeps track of all administrative promotions with time stamps and user description.
Nevertheless, events at WordPress level must need additional monitoring and log registration to supplement Kinsta Infrastructure.

Melapress offers an excellent solution here WP Activity Log. It records WordPress-specific events with minimal performance impact on the optimized environment of Kinsta.
With the help of the plug -you can configure notifications for critical security events such as new user creation, failed login attempts, plug -in or theme installations and even core file adjustments.
With Webhooks you can even connect notifications with the workflow tools of your team. For example, if you make a weak incoming webhook, you can then configure a WP activities log to send structured notifications:
{
"event_type": "user_privilege_escalation",
"severity": "critical",
"user_affected": "[email protected]",
"role_change": "editor_to_administrator",
"timestamp": "2025-08-10T14:30:00Z",
"site": "client-production.kinsta.cloud"
}
The payload will identify the user who takes the action and you can assess and respond quickly. You can also implement some other tools to help with your security monitoring:
- Head wp Aggregate security events in your portfolio, so that you can implement it on a special Kinsta site to check all your sites. The extension of the activity log extension through to SIEM platforms for business security activities.
- Patchstack Offers vulnerability monitoring with real -time reports. When vulnerabilities influence your sites, you will receive immediate notification with remediation guidelines. Testing of patches is a great use case for the staging environments of Kinsta before production of production.
When configuring your log retention, start with 30 days before GDPR, 90 days for PCI DSS and a year for hipaa. For long -term retention, it is also a good idea to export logs to Google Cloud Storage.
Use WP-Cli and Kinsta to check your security
Each Kinsta environment comprises WP-Cli installed in advance and accessible via SSH. This makes rapid auditing of security and emergency aid possible, which would otherwise last hours due to other interfaces.
The WordPress Developer sources for WP-Cli Can help you build systematic audits by using specific assignments. For example the WP user list Command filters per roll, while database questions find temporary patterns:
#!/bin/bash
# Monthly user security audit
echo "=== Administrator Accounts ==="
wp user list --role=administrator --fields=ID,user_login,user_email --format=table
echo "=== Recently Created Users ==="
wp db query "SELECT user_login, user_registered FROM wp_users
WHERE user_registered > DATE_SUB(NOW(), INTERVAL 30 DAY)"
The script identifies security risks in your user stock, such as unauthorized admin accounts and suspicious patterns for making users.
Use of the WP Core Verify-Checksums Assignment, you can check WordPress Core files for official checksums. This detects unauthorized changes that can indicate a compromise:
#!/bin/bash
# Daily integrity check
core_check=$(wp core verify-checksums 2>&1)
if echo "$core_check" | grep -v "Success"; then
echo "Alert: Core files modified"
# Send notification to team
fi
However, when a compromise takes place in rare cases, you can implement a Lockdown script to neutralize threats and at the same time retain the evidence:
#!/bin/bash
# Emergency lockdown script
# Step 1: Preserve evidence
echo "Creating forensic backup..."
wp db export emergency_backup.sql
tar czf site_snapshot.tar.gz ~/public
# Step 2: Block public access
echo "Enabling maintenance mode..."
wp maintenance-mode activate
# Step 3: Revoke admin privileges
echo "Removing administrative access..."
wp user list --role=administrator --field=ID | while read userid;
do
wp user set-role $userid subscriber
echo "Revoked admin: User ID $userid"
done
# Step 4: Force re-authentication
echo "Invalidating all sessions..."
wp config shuffle-salts
Each step serves a specific goal: it retains proof of the infringement of investigation, prevents access to stop further damage, draws privileges to neutralize the threat and makes the session invalid to force authentication again.
Multisite Supervision with Mykinner and external dashboards
Managing dozens of WordPress sites often requires that you combine mykinner infrastructure controls with WordPress management platforms. Mykinner offers bulk actions such as updates, backups and cache that is erased throughout your portfolio (supported by the activity log).
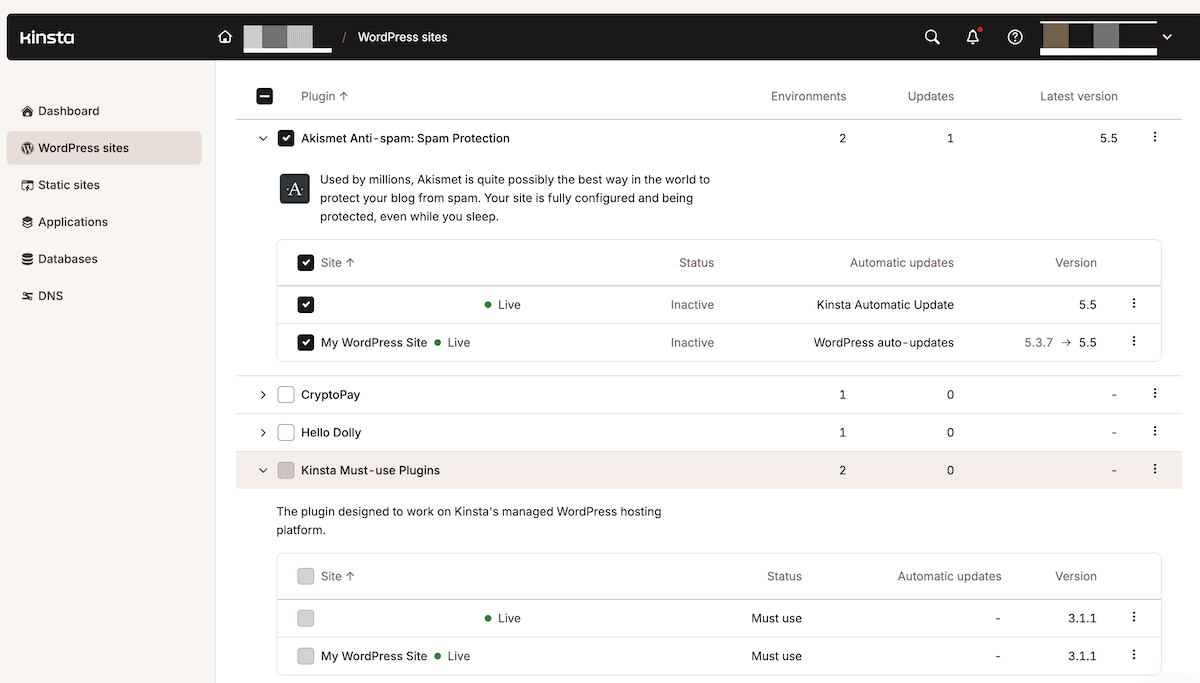
The indigenous functionality of Kinsta will be central to your security foundations:
- Bulk promotions for simultaneous operations on sites.
- Activity log registration for extensive audit paths.
- Custom labels for organizing sites per customer or security layer.
- API access for programmatic control.
You can also expand this with other WordPress -Management platforms:
- MainWP can offer you more than just login functionality. It can be implemented on your Kinsta plan and help you manage your portfolio as ‘child’ sites. The tool has vulnerability scanning, centralized plug -in management, monitoring of file integrity, bulk hardization and extra options.
- Management wp Works like a software such as a service (SaaS) solution for WordPress Multisite and makes a connection via a plug -in from the employee. The premium offer adds real-time scanning and white label reporting.
You can even consider using the Kinsta API to build custom security dashboards. Here is a simple and Barebones way to start it:
// Kinsta API security monitoring
async function checkSitesSecurity() {
const response = await fetch('https://api.kinsta.com/v2/sites', {
headers: {
'Authorization': `Bearer ${process.env.KINSTA_API_KEY}`
}
});
const sites = await response.json();
// Check each site's security status
return sites.map(site => ({
name: site.name,
ssl_active: site.ssl?.status === 'active',
php_current: parseFloat(site.php_version) >= 8.0,
backup_recent: site.backups?.[0]?.created_at > Date.now() - 86400000
}));
}
However, if you implement this, you must ensure that you look out for important infrastructure protection indicators: checking SSL statuses, PHP versions and back -upness.
Developing customer -oriented security transparency
Regardless of what you implement, customers want and need evidence that their investment offers protection. Having a policy of transparency when it comes to your security facility builds trust and justifies the maintenance contracts you have.
The structure and presentation of your reports is due to you. However, look at analysis and statistics to demonstrate both infrastructure and application security. For example, you can provide infrastructure statistics from Kinsta:
- Uptime percentage and incident history.
- DDOS attempts blocked by Cloudflare.
- SSL certificate status and extension data.
- Back -up success rates and availability.
- PHP version and security patches.
Van WordPress can take your statistics:
- The number of failed login attempts blocked.
- Vulnerabilities that you have discovered and patched.
- Following changes to user rights.
- Results for verification of file integrity.
- Security scan results.
Depending on the report you need, business statistics can also be useful. For example, it can make a list of the income that you have protected during attacks, how you have retained compliance, the availability of the site and much more.
Some customers may need real -time visibility, which can be easier to implement than you think. With the help of the WordPress role and the capacity system you can, for example, create limited access protocols:
/**
* Create client security viewer role
* Based on WordPress Roles and Capabilities documentation
*/
function create_security_viewer_role() {
remove_role('security_viewer');
add_role('security_viewer', 'Security Viewer', array(
'read' => true,
'view_security_reports' => true,
'view_activity_logs' => true
));
}
add_action('init', 'create_security_viewer_role');
/**
* Restrict viewer access to sensitive areas
*/
function restrict_viewer_access() {
$user = wp_get_current_user();
if (in_array('security_viewer', $user->roles)) {
$restricted = array('plugins.php', 'themes.php', 'users.php');
$current = basename($_SERVER['SCRIPT_NAME']);
if (in_array($current, $restricted)) {
wp_redirect(admin_url('index.php'));
exit;
}
}
}
add_action('admin_init', 'restrict_viewer_access');
The end result of this implementation creates one Viewer Roll with limited possibilities. This allows you to offer real -time security monitoring to customers and at the same time prevents critical changes during browsing.
Summary
Building effective WordPress security work flows on Kinsta needs both infrastructure and application layers of protection.
Kinsta offers the basis through its insulated container technology, Cloudflare WAF, mandatory 2FA and monitoring functionality. Workflows at WordPress level need extra plug-ins to fill in the empty spots, but a complete security architecture is more than possible.
Some of these tools also integrate seamlessly with the infrastructure of Kinsta. For example, you can have WP-Cli on every server, APIs for automation and bulk operations for efficiency.
If you are ready to build WordPress security workflows from Enterprise quality, explore the managed WordPress hosting of Kinsta and discover how the correct infrastructure protection makes protection manageable.
#WordPress #Security #Workflows #Kinsta #Implementation #guide




