Here are the top cybersecurity stories of the week.
- North Korean hackers targeted blockchain developers to steal crypto.
- The FBI has dismantled ransomware’s ‘last refuge’.
- Hackers have hacked single sign-on systems to target businesses.
- CISA’s acting chief caused a scandal by uploading agency documents to ChatGPT.
North Korean hackers targeted blockchain developers to steal crypto
North Korean hacking group Konni used AI-generated malware to attack blockchain developers, Check Point analysts said.
The main goal of the attackers is to gain access to development environments and thus open a path API credentials, infrastructure and ultimately crypto wallets of companies.
Experts say the attack starts on Discord, where the victim receives a link to a ZIP archive. Inside are a PDF decoy and a malicious LNK file. Launching the shortcut sets off a complex chain:
- A PowerShell loader starts and opens a DOCX document to distract the user.
- In the background, a CAB archive is unpacked with a backdoor, batch files (BAT), and a tool to bypass user account control.
- An hourly task is created in the scheduler, disguised as a OneDrive process, which runs a coded script directly in memory and erases traces after execution.
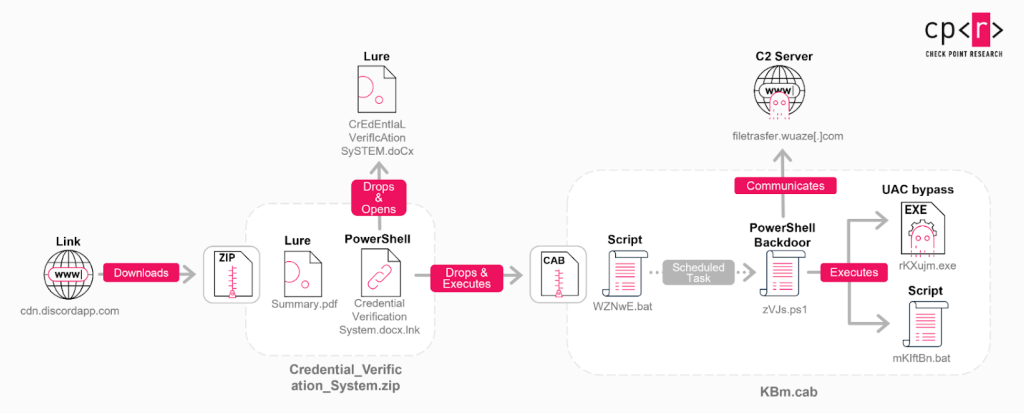 Infection chain. Source: Checkpoint.
Infection chain. Source: Checkpoint.Analysts concluded that the malicious script was created using a LLM. Several factors point to this:
- an unusual structure. Clear documentation at the beginning of the code and a neat, modular layout that is rare in “handcrafted” malware;
- comment. The code contains the line # < — — your permanent project UUID (your permanent project UUID).
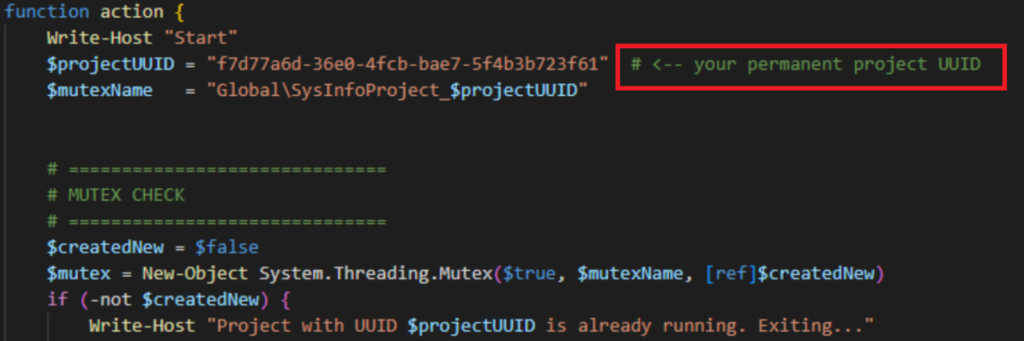 Source: Checkpoint.
Source: Checkpoint.Researchers linked the campaign to Konni based on similarities in loader formats and filenames used in previous operations.
The group has been active since 2014 and typically focuses on South Korea, Russia and Europe. The new campaign focuses on three countries in Asia and the Pacific: India, Japan and Australia.
The FBI has dismantled ransomware’s ‘last refuge’
The FBI, in collaboration with the US Department of Justice, has seized the popular cyber extortion forum RAMP, BleepingComputer reports.
RAMP billed itself as the “last refuge” for ransomware operators and attracted numerous groups that used the forum to recruit affiliates and buy and sell access to corporate networks.
Although there is no official statement yet, the domain’s DNS servers have been switched to the servers the FBI typically uses during seizures:
- ns1.fbi.seized.gov;
- ns2.fbi.seized.gov.
An administrator known as Stallman confirmed the development, acknowledging that years of his work had been wiped out.
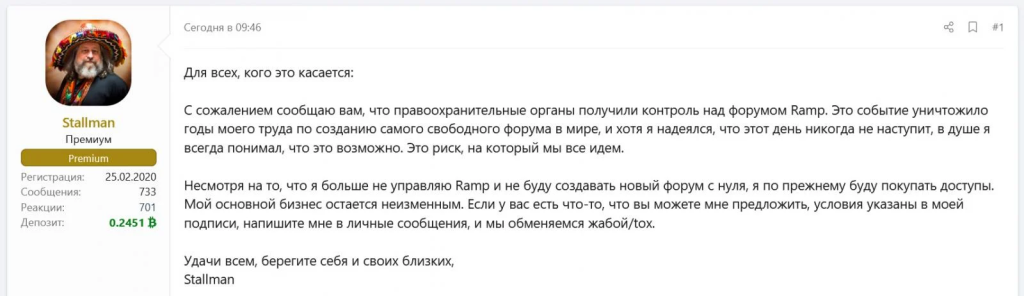 Screenshot from the XSS hacker forum. Source: BleepingComputer.
Screenshot from the XSS hacker forum. Source: BleepingComputer.According to the newspaper, law enforcement obtained a huge amount of confidential data: users’ IP addresses ($1.70), private messages and mailboxes. For forum participants who failed to maintain strict anonymity, this poses an immediate risk of de-anonymization and arrest.
The platform emerged in 2021 after other hacker portals such as Exploit and XSS banned ransomware advertisements. The source is controlled by hacker Mikhail Matveev, known as Orange.
 Source: FBI.
Source: FBI.In 2023, the US Department of Justice accused Matveev of involvement in the development of the Babuk, LockBit and Hive malware. He was added to the FBI’s Most Wanted Cybercriminals list and in November 2024 he was arrested in Kaliningrad.
Hackers have hacked single sign-on systems to target businesses
The ShinyHunters group launched a major wave of wishes attacks targeted single sign-on (SSO) systems from Okta, Microsoft and Google, the hackers told BleepingComputer.
The attackers use advanced social engineering: they call agents posing as support and convince them to enter logins and codes on spoofed sites.
An Okta report confirmed the use of advanced phishing kits. These tools include a web control panel that allows the hacker to modify the site’s content in real time while talking to the victim over the phone:
- if the attacker requires a code when entering the stolen credentials, a corresponding field will immediately appear on the victim’s screen;
- If push approval is required, the phishing site will display instructions on how to approve it.
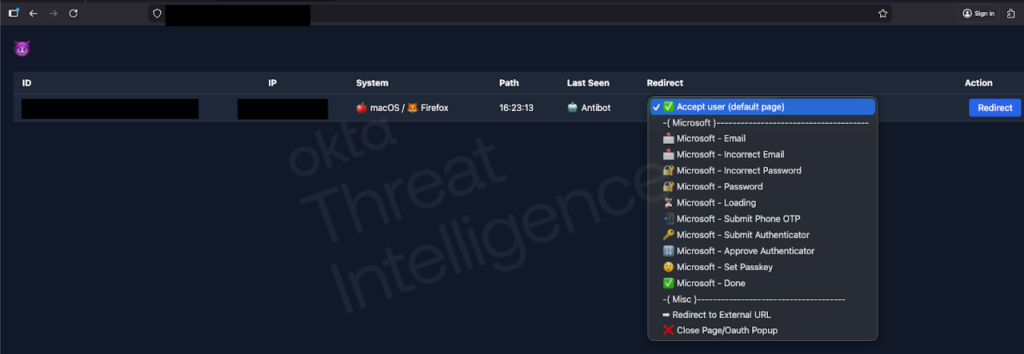 Hacker Rapid Response Toolkit. Source: Okta.
Hacker Rapid Response Toolkit. Source: Okta.Compromising a single SSO account can give criminals access to an entire business ecosystem, including Google Workspace, Slack, and Microsoft 365. To prepare their attacks, ShinyHunters use data from previous breaches (names, roles, and phone numbers) making their calls highly convincing.
The group also relaunched its leak site and posted breach data on SoundCloud, Betterment and Crunchbase. Representatives of the companies confirmed the incidents.
CISA chief makes waves by uploading agency documents to ChatGPT
Acting director of the US Cybersecurity and Infrastructure Security Agency (CISA) Madhu Gottumukkala became the subject of an internal investigation after he uploaded sensitive contract documents from the agency to ChatGPT, Politico reports.
Most CISA employees don’t have access to the chatbot, but Gottumukkala requested special permission to use OpenAI’s product instead of approved secure tools.
According to media reports, the federal network security system has issued several warnings about data breaches. Although the uploaded information was unclassified, it was marked as ‘for official use only’. The data can now be used by the model to respond to users, compromising the confidentiality of government contracts.
Gottumukkala could face discipline ranging from a formal reprimand to loss of clearance for classified information.
Cyber attack on the Polish energy sector: new details
In late December, Poland’s energy infrastructure was hit by a coordinated attack targeting distributed energy facilities across the country. The strikes affected thermal power plants and wind and solar energy systems, Reuters reports.
Although the attackers compromised operating systems and “irreparably damaged key equipment,” they failed to disrupt electricity supplies. The total capacity of the affected assets amounted to 1.2 GW, equivalent to 5% of Poland’s power supply.
Officially, twelve facilities were affected. However, cybersecurity firm Dragos said the actual number was as many as 30.
Researchers attributed the attack “with moderate confidence” to the Russian hacking group Electrum. Although its activity overlaps with the well-known Sandworm (APT44), the team classified it as a separate cluster.
Electrum was previously linked to attacks on Ukrainian networks using the Caddywiper and Industroyer2 malware. In Poland, the hackers have deployed a new one windshield wiper—DynoWiper.
According to Dragos, the attackers showed deep knowledge of industrial equipment. They deliberately focused on:
- vulnerable transmission and communications systems;
- remote terminals and border network devices;
- Windows-based monitoring and operating systems.
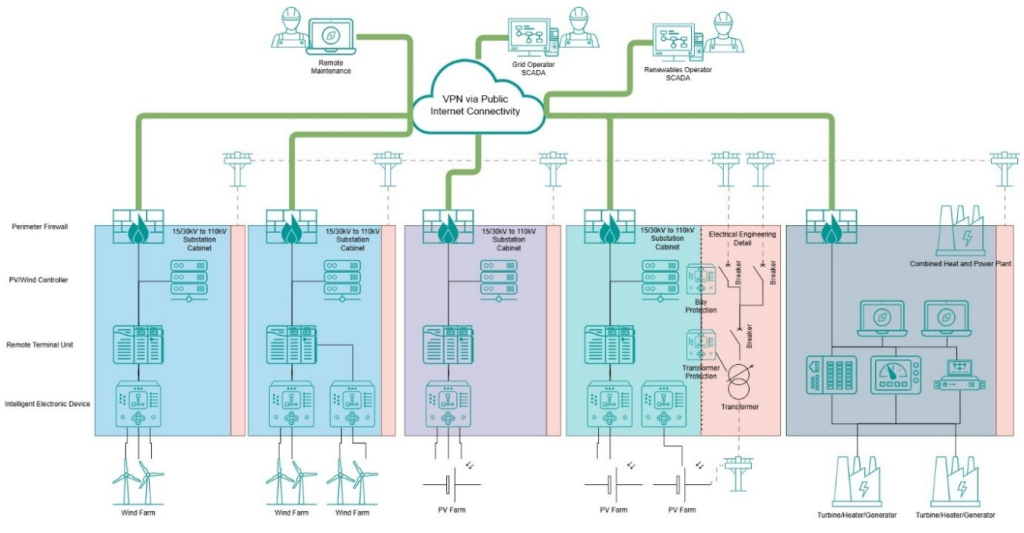 Diagram of the infrastructure of a sustainable energy system. Source: Dragos.
Diagram of the infrastructure of a sustainable energy system. Source: Dragos.The hackers successfully disabled communications equipment in several locations, leaving operators without remote control, although generation continued in autonomous mode.
Experts believe the shutdowns did not lead to a blackout. However, a sudden drop of 1.2 GW could have caused a critical frequency deviation. Similar fluctuations have led to successive failures in other countries, including the large-scale collapse of Iberia’s energy system in 2025.
Also on ForkLog:
- The US Department of Justice has seized $400 million from Bitcoin mixer Helix.
- Hackers stole $2.9 billion worth of cryptocurrency in 2025.
- Critical vulnerabilities have been found in the Clawdbot AI agent.
- Bragging on Telegram helped expose the theft of $40 million from the US government.
- ZachXBT accused Circle of inaction after the $16.8 million SwapNet hack.
What to read this weekend?
Vasily Smirnov unpacks the UN Hanoi Convention on Cybercrime. In his new piece he explores how signatory countries could apply it.
#FBI #Shuts #Ransomwares #Refuge #CISA #Chief #Uploads #Agency #Documents #ChatGPT #Cybersecurity #News #BitRss #Crypto #World #News



