In the current age of software – wild growth, the primary challenge does not take on new tools – it is to check who they can use, how they are used and when access should end.
Most companies can be managed 300–400+ Apps at a certain moment, and without consistent Identity and access management (IAM)Security gaps can multiply. Forgotten accounts, ad-hoc permission and unclear ownership do not only delay teams-do not expose organizations to real risk.
WebFlow Enterprise Takes a holistic approach to IAM, designed to give companies that every step of the access cycle is safe and automated. Provide new users, manage authentication, apply detailed access controls, use usage use and use deprovisioning to offboarding – we have built governance into any layer of the product.
By weaving IAM directly into the web flow experience, we enable companies to scale up web creation without endangering supervision. Teams are given the freedom to work together, while IT and security teams retain the certainty that access is always accurate, auditable and in accordance with the company policy.
The Lifecycle of WebFlow Identity and Access Management (IAM)
Most IT organizations of companies evaluate Saas platforms via the lens of IAM because any phase of user life cycle of users, from onboarding to offboarding, offers a chance of risks if it is not managed correctly. It is not enough to offer insulated functions – trust is built when a platform supports the entire life cycle:
- New users
- Authentic access
- Authorizing the right level of permissions
- Monitoring user activity
- Access to access when employees leave
WebFlow’s Enterprise-Grade offers maps directly to this framework. Let’s see what you get in every phase of the life cycle.
1. Provisioning: safe and seamless to boarding
Manual onboarding does not scale and it creates risk. IT teams need automated, standardized ways to get employees in tools quickly and safely. By adopting the same standards that it already uses over hundreds of apps, WebFlow fits seamlessly into existing identity workflows.
WebFlow supports company provision in two ways:
This gives companies a scalable, safe way to get employees to web flow without bothering them.
“We manage hundreds of apps, and as our company grows, it is crucial that we can easily create and remove user accounts, so that the right people have access to the right tools at the right time – all centrally managed by our IDP. And that is what we get with automated scim facility and a security perspective.
– Sid Bhargava, Sr. Enterprise Security Engineer at WebFlow
2. Authentication: strong frontline defense
Authentication is the first line of defense for enterprise security teams. And for most large organizations – Including 72% of the Fortune 500 companies -Single Sign-On (SSO) is a requirement in how they evaluate and accept new applications.
WebFlow offers several verification layers to adjust to those standards:
Together they reduce the dependence on individual references and vote web flow with Enterprise Security Baselines.
3. Authorization: the least privileges on scale
One of the greatest risks in Enterprise environments is to give over-permission users more access than they need. That is why most IT teams look for tools that offer detailed controls to adjust access to their needs.
WebFlow supplies with multiple layers of detailed authorization controls:
.png)
With these checks, organizations can scales their teams in a responsible manner, so that growth is matched with the demand from the board and the safety of today.
“We work in a highly regulated industry where robust compliance and risk management are of vital importance. Being able to create adapted roles for things like ‘Designer – can only be able to publish to Staging’ to keep us the opportunity to publish to production up to a select number and protect our production site.”
– Adam Jones, head of digital marketing at L&C Mortgages
4. Monitoring: visibility and compliance
Visibility in what happens and who does what is non-negotiable for IT teams from Enterprise, with 90% of the security leaders Sharing SEEM systems (Security Information and Event Management) are essential for their activities.
WebFlow Enterprise offers two layers of monitoring:
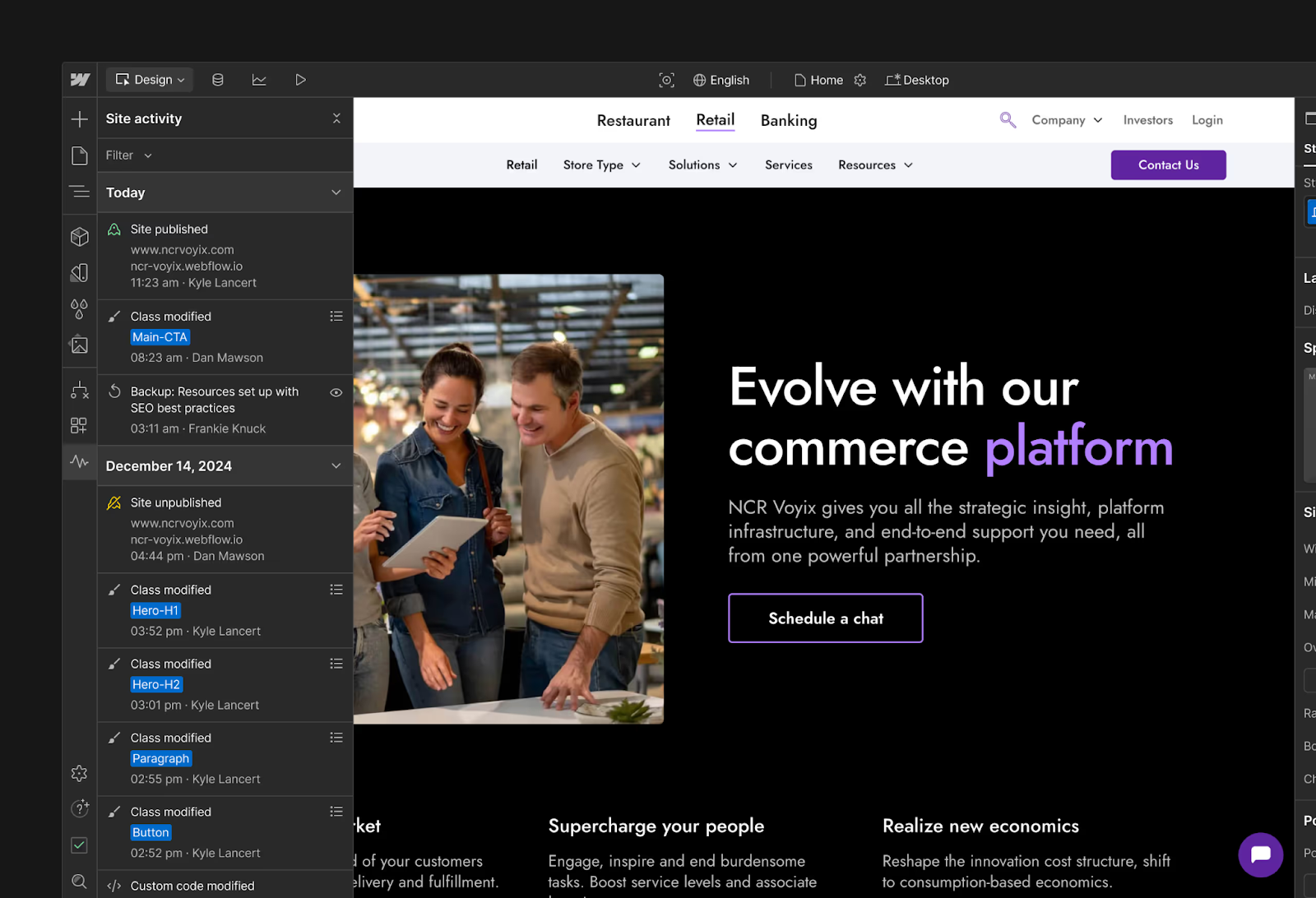
- Site Activity Log: Follow it what, when and who for important changes in the site, so that you can solve problems faster.Europ
- Auditlogi -Api: Exportable logs that follow important user events for compliance and monitoring – such as login activity, rolling and consent changes and more – that security and IT teams can take in monitoring dashboards and Siem Tools.
This gives security and the team the traceability they need to meet the compliance requirements and to respond quickly when problems occur.
5. deprovisioning: Close the loop
The lifecycle of the users ends with offboarding and it is one of the risky times if it is not managed properly. Persistent reports can often become goals for attack.
WebFlow offers automated off -boarding via:
- SCIM -Deprecification: Remove automatic access when employees leave or change, so that permissions are tightly tailored to HR and IT systems.
Security and IT teams can be sure that when platform access had to end in web flow, it really does.
Build trust as a basis, not a function
We know that companies and security leaders not only evaluate whether a platform can host content, evaluate them whether it can be controlled on a scale.
By investing in the Lifecycle of Identity and Access Management (IAM), WebFlow makes it easier for companies to automate, protect and scale how they manage access, so that you can concentrate on the driving results for your company, not on manual administrator work.
This is not the end of the trip. As companies evolve, our investments in governance and trust that are, will ensure that WebFlow remains a platform and can trust security leaders with trust.
If you want to talk to someone about access to the above options on WebFlow Enterprise, Contact our sales team.
#Balancing #Trust #Access #Control #Webflow #Enterprise #WebFlow #Blog




